NTH Éire
 I recently became a member of the International Cyber Threat Task Force (ICTTF), headquarted in Dublin Ireland, and am expanding NOWHERETOHIDE’s business and government service offerings to Ireland and other European government and private sector organizations.
I recently became a member of the International Cyber Threat Task Force (ICTTF), headquarted in Dublin Ireland, and am expanding NOWHERETOHIDE’s business and government service offerings to Ireland and other European government and private sector organizations.
7/5/2011 Update
- My presentation at the 2011 Cyber Threat Summit at the Dublin Convention Centre was a huge success; you can see my presentation here –> Cyber Threat Summit Chuck Georgo Presentation (v3) 20110629
- I was also interviewed by RTE about cyber threats and social media, you can hear my interview at this link – CLICK ME.
7/8/2011 Update
- Link to newspaper article “Cybercrime just all to easy” that speaks about Cyber Threat Summit and quotes me http://www.irishtimes.com/newspaper/finance/2011/0708/1224300295547.html.
8/14/2011 Update
- Video presentation of my introduction of the U.S. InfraGard Program to Europe, given at the July 5, 2011 Cyber Threat Summit in Dublin, Ireland:
8/31/2011 Update
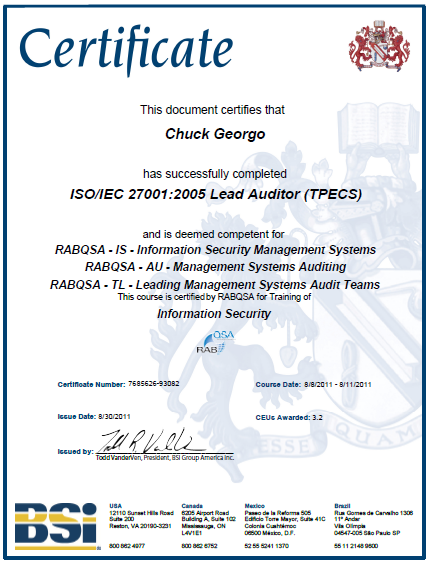 NOWHERETOHIDE.ORG completes ISO/IEC 27001:2005 Lead Auditor (TPECS) competency, now prepared to help Irish and other EU organizations improve their Information Security Management Systems.
NOWHERETOHIDE.ORG completes ISO/IEC 27001:2005 Lead Auditor (TPECS) competency, now prepared to help Irish and other EU organizations improve their Information Security Management Systems.
The British Standards Institute (BSI) issued ISO/IEC 27001:2005 Lead Auditor (TPECS) certificate to Chuck Georgo today. ISO/IEC 27001ISO/IEC 27001 is an Information Security Management System (ISMS) standard published in October 2005 by the International
Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC).
ISO/IEC 27001 formally specifies a management system that is intended to bring information security under explicit management control. Being a formal specification means that it mandates specific requirements. Organizations that claim to have adopted ISO/IEC 27001 can therefore be formally audited and certified compliant with the standard.
NOWHERETOHIDE will be publishing a series of blog posts over the next few weeks to help educate organizations about the standard, its criteria, and strategies for achieving compliance.
6/22/2012 Update
Love Guiness? Hate Cyber Crime?
Get on a plane and join me at International Cyber Threat Task Force (ICTTF) Cyber Threat Summit in Dublin, Ireland 20/21 September 2012, be my guest by using the registration code: nowheretohideguest – http://www.cyberthreatsummit.com/
10/21/2012 Update
Cyber Threat Summit – Dublin, Ireland
Why can’t Johnny be good? The making of an insider threat
“When Johnny reports to work for you on Day 1, they DO NOT intend to do you or your organization’s information systems any harm; something happens to them, either in their personal or work life that changes this – the CEO’s or Agency Head must be held responsible for making sure they know what’s going on with all of the Johnnys (and Janes) in their organization to prevent the good people they hired from becoming insider threats.”
While most of the world is focusing on “technology” as a solution to preventing insider threat attacks to organization/agency information and systems, hardly anyone is focused on leadership’s responsibility to create and sustain a work environment that minimizes the chance for an employee to turn into an insider threat.
On October 21, 2012, I had the chance to speak on this issue at the 2012 International Cyber Threat Task Force (ICTTF) Cyber Threat Summit in Dublin, Ireland a few weeks ago; here is a video recording of my presentation, I hope you find it informative and useful.
10/1/20125Update
Cyber Threat Summit – Dublin, Ireland
Message to the Board: Stop being an Ostrich when it comes to cyber security – Trust, but Verify
I just gave this presentation to nearly 200 attendees of the ICTTF Cyber Threat Summit 2015 in Dublin, Ireland.
For those of you that attended; thank you!
Through this presentation I hope I was able to communicate three points:
- How company/agency executives put their agencies at risk by blindly trusting that they are doing all that can be done to secure their networks, applications and data;
- That leadership’s approach to motivating employee’s to practice better cyber hygiene needs to mimic principles of behavioral economics theory that advertisers use; and
- By changing the way they ask questions to their senior staff (mainly their CIO/CISO), they can a) have better proof that necessary cyber protections are in-place, and b) they will have a better understanding of the unaddressed cyber risk their company/agency faces.
Enjoy…r/Chuck
10/24/2018 Update
European Union (EU) Cyber Threat Summit – Dublin, Ireland
CISOs: Tired of pushing the cybersecurity rock up that hill?
I just gave this presentation to nearly 2,000 attendees of the ICTTF EU Cyber Threat Summit 2018 in Dublin, Ireland.
For those of you that attended; thank you!
Enjoy…r/Chuck
