Law enforcement information sharing
02.03.2013
Budget, congress, criminal justice, Data, data sharing, Information sharing, justice, law enforcement, Law enforcement information sharing, leadership, LEIS, N-DEx, NIEM
If you want law enforcement agencies to share information, go to the source and help the Chiefs and Sheriffs to push their data in the FBI’s National Data Exchange N-DEx. Trying to impose information sharing with unfunded standards mandates will not work.
As someone who has been in the standards business since 1995, history has proven to me that:
- The business need must drive standards, standards can NEVER drive the business; and
- Trying to SELL the business on standards is a losing strategy.
Hi Congressman Reichert,
You won’t remember me, but a long time ago we were in meetings together in Seattle with the likes of John McKay, Dave Brandt, Scott Jacobs, Dale Watson, and others working on building the Law Enforcement Information Exchange (LInX); I was the technical guy on the project, working with Chief Pat Lee and our very dear lost friend Julie Fisher (may she rest-in-peace, I sure miss her).
A hell of a lot of water has gone under the bridge since then–it’s been nearly TWELVE YEARS. If we look back over this time, we have had so many bills, laws, strategies, policies, papers, speeches, conferences, proclamations, and other assorted attempts to prod law enforcement data loose from the nearly 18,000 agencies across our country. While we are far better off than we were back then, I think we can agree that we still have a long way to go.
Where we differ, I’m afraid, is in the approach to get there – a few days ago, you proposed legislation, the Department of Justice Global Advisory Committee Authorization Act of 2013, as a means to improve information sharing among law enforcement agencies – do we really believe another “stick” will work to get agencies to share information? Do we really believe it’s a technology or data standards problem that’s preventing law enforcement data from being shared? As a technologist for 34 years, and someone who has been involved in law enforcement information sharing since the Gateway Project in St. Louis, MO in 1999, I can tell you it is neither.
While I applaud the work of the GAC, and I have many colleagues who participate in its work, I’m afraid having more meetings about information sharing, developing more standards, approving more legislation, and printing more paper will NOT help to reach the level of information sharing we all want.
Instead, I want to propose to you a solution aimed at capturing the commitment of the men and women who can actually make law enforcement information sharing happen, and virtually overnight (metaphorically speaking) – namely, the great men and women who lead our police and sheriffs departments across America.
Now to be fair, many of these agencies are already contributing their records to a system I am sure you are familiar with called the National Data Exchange (N-DEx). Built by the FBI CJIS Division, this system has matured into a pretty respectable platform for not only sharing law enforcement information, but also for helping cops and analysts to do their respective investigative and analytic work.
Now, in case you are wondering, I do not own stock in any of the companies that built N-DEx, nor has the FBI signed me up as a paid informant to market N-DEx. I write to you on my own volition as a result of my nearly six years of volunteer work as a member of the International Association of Chiefs of Police (IACP) Criminal Justice Information Systems (CJIS) Committee.
About two years ago I volunteered to lead a small sub-group of the committee who have either built, led, or managed municipal, state, federal, or regional information sharing systems. Our charge was (and still is) to help CJIS take a look under the hood of N-DEx to see what’s in there (data wise) and to help figure out what needs to be done to make it a more effective tool to help cops across America catch more criminals, and maybe, just maybe, even prevent criminals from acting in the first place.
While our work is far from done, I can tell you that one thing we need is more data – as you well know, be it N-DEx, LInX, RAIN, or any other information sharing system, it is only as good as the data that’s put into it.
Believe it or not we already have the data standards in-place to get the data into N-DEx. CJIS has developed two Information Exchange Packet Descriptions (IEPDs) that tells agencies exactly what to do and how to format and package up their data so it can get to N-DEx. Additionally, CJIS has an extensive team ready to assist and my colleagues over at the IJIS Institute hold training sessions sponsored by BJA, to help agencies along the process (NIEM training).
These two IEPDs can help law enforcement agencies today to share the following law enforcement records:
- Service Call
- Incident
- Arrest
- Missing Person
- Warrant Investigation
- Booking
- Holding
- Incarceration
- Pre-Trial Investigation
- Pre-Sent Investigation
- Supervised Release
So what’s the hold up? Speaking only for myself, and I will be very straight with you, I believe the root cause for not getting more law enforcement data into N-DEx is the current piecemeal, politically charged, hit and miss grant funding process that the Act you propose, if passed, will burden even further – see page 3, lines 17-25 and page 4, lines 1-6.
Instead, I ask that you please answer the following question…
If law enforcement information sharing is important enough to push though a Public Act, where is the nationwide project, with funding, to get all shareable law enforcement data loaded into the one system that would give ALL law enforcement officers and analysts access to collective knowledge of the nearly 18,000 law enforcement agencies?
The immediate answer might be “we already have one; N-DEx;” however, N-DEx is only a piece of the answer…it’s as they say, “one hand clapping.” And in all fairness to my friends and colleagues at the FBI CJIS Division, that program was only charged and funded to build the N-DEx bucket, they were never funded to actually go get the data to fill the bucket.
The strategy, for whatever reason back then, was relegated to a “build it and they will come” approach, that IMHO has not worked very well so far and may take another 5-10 years to work. I should also note that the bucket isn’t totally empty…there are quite a number of agencies and regional projects, like LInX, that have stepped up and are helping to fill the bucket – however, if we want to expedite filling up the bucket, focusing on mandating more standards is not the answer
What I submit is the “other hand clapping” is the need for a shift focus, away from policy, standards, and technology, and establish a funded nationwide project that will offer a menu of choices and support packages to the Chiefs and Sheriffs that will enable them to start sending as many of their shareable records as possible to N-DEx.
Some of the options/support packages could include:
- Provide direct funding to agencies and regional information sharing systems to develop N-DEx conformant data feeds to N-DEx;
- Grant direct funding to RMS and CAD system providers to develop N-DEx conformant data feeds from their software, with the stipulation they must offer the capability at no additional cost to agencies that use their products;
- Establish a law enforcement data mapping assistance center, either bolted on to IJIS NIEM Help Desk, as an extension of NLETS menu of services, or through funding support at an existing information sharing project like the Law Enforcement Technology, Training, & Research Center who works in partnership with the University of Central Florida.
At the end of the day, we all know that the safety and effectiveness of law enforcement is greatly affected by the information he or she has at their fingertips when responding to that call.
Do you really want to leave it to chance that that officer’s life is taken, or a criminal or terrorist is let go because his or her agency wasn’t “lucky enough” to win the grant lottery that year?
So, let’s empower the single most powerful force that can make sure the information is available – the Sheriff or Chief leading that agency. Let’s stop with the unfunded mandates, laws, standards, studies, point papers, etc., and let’s finally put a project in-place with the funding necessary to make it happen.
v/r
Chuck Georgo,
Executive Director
NOWHERETOHIDE.ORG
chuck@nowheretohide.org
02.06.2012
law enforcement, Law enforcement information sharing, LEIM, public safety, Uncategorized, video
 Hi everyone,
Hi everyone,
My Name is Mary Wood and I recently joined NOWHERETOHIDE.ORG as a Research Analyst. I am from Dublin, Ireland, and new to Public Safety, so be gentle with me! These first few blog postings will tell the story of my experience at the 2012 Law Enforcement Information Management (LEIM) conference that I attended from 19-23 May 2012.
Since this was my first time attending LEIM, I didn’t really know quite what to expect. What I experienced was a whirlwind three days of educational sessions and networking opportunities – I really enjoyed everything about this conference and learned so very much!
I was also in awe of being in the presence of the brave men and women who put their lives in danger every day just to keep the rest of us safe – that in itself was daunting. But as I walked around, amongst Officers, Chiefs of Police, federal agents, and even a British Lord!, I was stuck by the camaraderie and incredible respect they had for each other. I really love Americans, and have always found them to be extremely polite and well mannered, and these three days showed just that, and also an enthusiasm for learning, meeting new people, and sharing of their experiences with dealing with information management in the public safety arena.
I found myself learning something new with each presentation/workshop that I attended. I was very impressed by the high standard of presenting styles and the way most people I encountered delivered their information in a very understandable (essential for a first timer!) and enjoyable way.
I learned quite a bit – using CCTV effectively, getting essential data into systems so Police Departments in other states can access it, predictive Policing, Social Media and how law enforcement agencies use the social media sites to gain information, the latest License Plate readers, what happens when a Police Officer wears a camera, and many more interesting ways that technology is used everyday.
Yes, law enforcement information management has come a long way from the pencil and notebook. Today the paper and pencil has been replaced by an iPhone or Blackberry to access/enter information, to take video and pictures, and to share information. I have learned that it is all about getting information and sharing that information to get the bad guys of the streets.
For any first timers to the LEIM conference next year, I would highly recommend that you arrive early enough to attend the First Time Conference Attendee Orientation and ABC’s of IT for Law Enforcement. This session will help answer any questions first timers may have about the conference. The LEIM Board of Officers together the LEIM Chairperson put on a very informative and straightforward presentation. They will also answer any questions put to them.
Ed Posey, the 2011-2012 Chairman, spoke about his work as a Captain in Gainesville Police Department. He spoke about the Law Enforcement Information Exchange (LInX) Lynx project and answered general IT questions put to him. Lance Valour talked about the way the Police Service works in Canada, and the differences between America and Canada (I loved his Canadian accent!), and Lance should know with 33 years in Ottawa Police Force behind him. They also explained how 9/11/01 changed everything in terms of security and getting essential information and sharing it, so everybody can work together and understand the situation they are dealing with. N-DEx was one of the information sharing systems that was created after 9/11/01. It is designed to share federal, state and local law enforcement information. The types of data being exchanged varies from police case files, arrest reports, warrants, Canadian and Interpol databases, and corrections data.
On the first day there are also other preconference workshops presented, along with the first timers conference. They are each three hours long, but are a must to explain any questions you have or any guidance you need to get you through the three days.
I have grown up, watching cop shows that show us how it’s done. We think we know it all, but it’s a lot different when you are in the presence of the people who really know how it’s done. I came away from my three days with a lot of information and pages and pages of notes, and also had the pleasure of being in the company of people who really do make a difference by making our world safer.
Over the next few blog postings I will share some stories about specific things I learned about…stay tuned.
Thanks for reading…r/Mary
05.04.2012
Data, data sharing, JIEM, Law enforcement information sharing, LEIS, NIEM
I posted this response to a question on the LinkedIn NIEM group where someone asked about the slow rate of NIEM adoption; i thought i would cros post my response here.
What’s standing in the way of NIEM adoption?It’s about leadership.
- It’s about reducing complexity.
- It’s about getting the word out.
- It’s about opening up proprietary protocols.
- It’s about conformance.
- It’s even about standards.
What’s really standing in the way? Two things…a) utility and b) a market for it.
I think it would also be wise for us to take a few pages out of the eCommerce, EDI, EBXML world (and honestly, the internet as a whole). EDI became a standard because large companies said “if you want to do business with me, then you will stop faxing me POs and start sending them to me in this new thing called EDI. When XML appeared on the scene the same companies converted their information exchanges to EBXML and vendors and service providers folllowed suit – one might say if it weren’t for the EDI-to-EBXML movement, we might not even be talking about GJXDM or NIEM today; EBXML was groundbreaking in ts day.
So what’s in the way? I’ll look at this in terms of two things I mentioned above:
- Utility of NIEM– The “technology Acceptance Model” tells us that for increased adoption of a technology, it must be “useful and easy to use.” Today, however, we are having difficulty getting people to see the utility of NIEM, and it certainly has not proven itself to be easy to use either. Now, to be fair, NIEM started off life as dictionary of common data elements (words if you will) with working views of syntax and semantics. Then we have IEPDs. These are like sentences strung together, and by different authors, and the difficulty is that we don’t have a good way to know how well those sentences are strung together, whether or not we can assemble those sentences into comprehensible paragraphs, or even what “stories”(and where in those stories) those sentences might belong. In other words, I don’t think NIEM is coupled tightly enough to the business processes of Justice and Public Safety agencies. To become more useful, we must dust off JIEM, revalidate the inventory of Justice exchanges, and specifically tie them to NIEM IEPDs. And while we do this, we must clean up the inventory of IEPDs, remove ones that are toublesome, and reference those IEPDs back to the Justice business process and exchanges in JIEM.
- A Market for NIEM– Unfortunately, reuse has NOT always result in cost savings. There are a number of examples where agencies have had bad experiences with implementing NIEM, whether it was because of lack of skill of the integrator, poor IEPD design, poor project planning, immature integration tools, or good old politics, saying an agency will save money by using NIEM is not a strong position right now. To resolve issue (after we join NIEM and JIEM) I think we must attack the problem at the root–in the technology acquisition process. Stop with the buttons and bumper stickers and neat shirts (I have one too). What we need to do is drive NIEM use through RFPs and contracting processes. Of course, we have to first clean up the clearinghoue, but then we must help agencies to craft RFP language that they can use to call for use of NIEM and “NIEM-enabled” web services to effect the information exchanges called out in the business processes to be suported by the new technoogy acquisition. While some vendors have demonstrated leadership in this area, the real driver (in a free market economy) is the contracting process–vendors will invest in their ability to adopt and integrate NIEM if it’s in their financial interest to do so–they do have payrolls to meet and investors to keep happy. Some shining light in this quest is also the effort by IJIS and others who are working hard to establish a “standards-like” effort to clean up IEPDs and to help vendors demonstrate conformance (or compliance) to those standards for their products.
Your comments/thoughts are welcomed….r/Chuck
02.06.2011
computer security, cyber security, data sharing, Information sharing, law enforcement, Law enforcement information sharing, LEIS, security, security threats, Uncategorized
 So it’s no great revelation that public safety has benefited greatly from public private partnerships, and I’m cool with that, especially when we are dealing with technology that saves lives. However, a press release hit my email inbox today that made me think of the risks to security and privacy when we implement innovative technologies.
So it’s no great revelation that public safety has benefited greatly from public private partnerships, and I’m cool with that, especially when we are dealing with technology that saves lives. However, a press release hit my email inbox today that made me think of the risks to security and privacy when we implement innovative technologies.
Before I get into the story it, let me be v-e-r-y clear…I am NOT here to debate the effectiveness or morality of red-light/speed enforcement systems, nor am I here to cast dispersions on any of the organizations involved in the press release…this blog posting is strictly about using the Gatso press release to emphasize a point about security and privacy – when we engage in innovative law enforcement technology solutions, we need to take extra care to adequately address the security and privacy of personally identifiable information.
Here’s the press release from Gatso-USA:
GATSO USA Forms Unique, Strategic Partnership with Nlets
Earlier this month, GATSO USA was approved as a strategic partner by the Board of Directors of the National Law Enforcement Telecommunications System (Nlets). Nlets is….general narrative about NLETS was deleted. The approval of GATSO is an exciting first for the photo-enforcement industry.
Nlets will be hosting GATSO’s back office and server operations within the Nlets infrastructure. GATSO will have access to registered owner information for all 50 states plus additional provinces in Canada. The strategic relationship has been described as a “win-win” for both organizations.
From Nlets’ perspective, there are key benefits to providing GATSO with hosted service. Most importantly, it virtually guarantees personal data security. Due to this extra step of storing personal data behind the DMV walls of Nlets, the public can be assured that security breaches — such as the recent incident with PlayStation users — are avoided.
From GATSO’s perspective, hosting the system with Nlets will provide a ruggedized, robust connection to comprehensive registered owner information — without the security issues faced by other vendors in this industry. Nlets was created over 40 years ago…more stuff about NLETS was deleted).
The main points I took away from this press release were:
- Nlets is going to host the back-end server technology that GATSO needs to look up vehicle registration information of red-light runners;
- Gatso is going to have access to vehicle registration information for all vehicles/owners in ALL 50 states in the U.S. and (some) provinces in Canada; and
- And, because it’s behind Nlets firewalls, security is not an issue.
Again, please don’t call me a party-pooper as I am a huge advocate for finding innovative ways to use technology to make law enforcement’s job easier. However, I am also painfully aware (as many of you are) of the many security and privacy related missteps that have happened over the last few years with technology efforts that meant well, but didn’t do enough to make sure that they covered the bases for security and privacy matters. These efforts either had accidental leakage of personal information, left holes in their security posture that enables direct attacks, or created opportunities for nefarious evil-doers with legitimate access to use that access to sensitive information for other than honorable purposes.
After I read the press release, I thought that it would be a good case-study for the topic of this blog – it involved innovative use of technolgy for law enforcement, a psuedo-government agency (Nlets), two foreign-owned private companies, and LOTS of PII sharing – some might even say it had all the makings of a Will Smith movie. 🙂
To help set the stage, here are a few facts I found online:
- Gatso-USA is a foreign company, registered in New York State, operating out of Delaware; its parent company is a Dutch company, GATSOmeter BVGatso.
- Gatso does not appear to vet all of the red-light/speed violations itself; it uses another company – Redflex Traffic Systems to help with that (Redflex is not mentioned in the press release).
- Redflex seems to be a U.S. company, but it has a (foreign) parent company based in South Melbourne, Australia.
- Finally, there are no-sworn officers involved in violation processing. Red-light/speed enforcement cameras are not operated by law enforcement agencies; they outsource that to Gatso, who installs and operates the systems for local jurisdictions (with Redflex) for free, (Gatso/Redflex is given a piece of the fine for each violation).
There are no real surprises here either; there are many foreign companies that provide good law enforcement technologies to jurisdications across the U.S., and outsourcing traffic violations is not new…BUT what is new here is that a sort-of-government agency (Nlets), has now provided two civilian companies (with foreign connections) access to Personally Identifiable Information (PII) (vehicle registrations) for the entire U.S. and parts of Canada…should we be worried?
Maybe; maybe not. Here are nine questions I would ask:
- Personnel Security: Will Nlets have a documented process to vet the U.S. and overseas Gatso and Redflex staff who will have access to this information through direct or VPN access to Nlets systems?
- Data Security: Will Gatso or Redflex maintain working/test copies of any of the registration information outside of the Nlets firewall? If so, are there documented ways to make sure this information is protected outside the firewall?
- Data Access: Will Gatso/Redflex have access to the entire registration record? or, will access be limited to certain fields?
- Code Security: Will any of the code development or code maintenance be done overseas in the Netherlands or Australia? If so, will all developers be vetted?
- Network Security: Will overseas developers/site suport staff have access to the data behind Nlets firewalls? What extra precautions will be taken to protect Nltes systems/networks from abuse/attack?
- Code Security: Will Nlets conduct any security testing on code loaded on the servers behind their firewalls?
- Stakeholder Support: Have all 50 U.S. states, and provinces in Canada, been made aware of this new information sharing relationship? Do they understand all of the nuances of the relationship? And, are they satisfied that their constituents personal information will be protected?
- Audit/Logging: Will all queries to vehicle registration information logged? Is someone checking the logs? How will Nlets know if abuses of authorized access are taking place?
- Public Acceptance: How do states inform their constituents that their personal vehicle registration information is being made available to foreign owned company? Will they care?
How these questions are answered will determine whether or not we should worry…
Did I miss any other important questions?
Beyond this particular press release and blog posting, I suggest that you consider asking these kinds of questions whenever your agency is considering opening/connecting its data systems to outside organizations or private companies—it may just prevent your agency from becoming a headline on tonights news, like St. Louis –> St. Louis Police Department computer hacked in cyber-attack .
The bottom-line is that whenever you take advantage of opportunities to apply innovative technologies to public safety, make sure that you cover ALL the bases to protect your sensitve data and PII from leakage, direct attacks, or misuse and abuse.
As always, your thoughts and comments are welcome.
r/Chuck
28.01.2011
data sharing, Information sharing, Law enforcement information sharing, LEIS
Almost two years ago, i responded to a blog posting by Jeff Jonas entitled “Nation At Risk: Policy Makers Need Better Information to Protect the Country.” After a recent discussion about law enforcement information sharing with a colleague, i thought it might be worthy to re-run my response here…read the posting below and let me know what you think…r/Chuck
March 17, 2009
Hi Jeff,
With sincere apologies to Sean Connery, I am dismayed that people are still bringing a knife to an information sharing gun fight—the importance of information sharing, data discoverability, security protections, metrics and incentives, and empowerment have been documented many times over since I became involved in information sharing in 1999 and have proved to be of little value to making information sharing happen.
I believe a significant reason for this is that information sharing has been seen as the “main thing.” Information sharing should NEVER be seen as the main thing; it is simply a means to an end. I have never forgotten what Scott McNealy of Sun Microsystems said—“The main thing is to keep the main thing the main thing.” And, the main thing for government is safe streets, clean air and water, a strong economy, etc…NOT information sharing.
The “guns” that we need to bring to the information sharing table are simply engaged executive leadership and accountability for mission results.
Of the many significant information sharing projects around the country that I have been a part of, I can tell you that the most important ingredient for successful information sharing is: “An agency executive who actively communicates an operational imperative for mission success and then holds their managers accountable for using information sharing as a critical enabler for achieving desired mission results.” [I have a few blog posts on the subject at http://www/nowheretohide.org/wordpress]
While I agree that good security, good technology, good project management, good metrics and the like are necessary, none of this will matter if the need for information sharing is relegated two or three levels down the organization chart or is just seen as an edict from above—federal, state, and municipal agencies are already choking on multiple (and often conflicting and unfunded) mandates.
With my apologies to our President, the PM-ISE, and the Markle Foundation there is nothing more they can print on a sheet of paper to make information sharing happen—hundreds of executive orders, national strategies, task force reports, and security policies have been published—what more could they possibly say?
I believe it now comes down to the individual will of executive leadership in those federal, state and municipal agencies who hold the information that should be made shareable and their capacity to make it happen within their respective agencies. And that Jeff is the one area where I do believe that President Obama and our Congress can help—by simply ensuring that the people they choose to lead those agencies a) truly embody the will, character, and leadership qualities to achieve the mission and b) understand the value that information sharing brings to help make that happen.
r/Chuck Georgo
chuck@nowheretohide.org
30.01.2010
data sharing, Information sharing, Law enforcement information sharing, privacy, security
 The Poneman Institute, considered the pre-eminent research center dedicated to privacy, data protection and information security policy, released its 2009 Ponemon Institute “Cost of a Data Breach” Study on January 29, 2010.
The Poneman Institute, considered the pre-eminent research center dedicated to privacy, data protection and information security policy, released its 2009 Ponemon Institute “Cost of a Data Breach” Study on January 29, 2010.
In the report, they published the results of their fifth annual study on the costs of data breaches for U.S.-based companies. They surveyed 45 companies represnting 15 various industry sectors–significant contributors were financial, retail, services and healthcare companies.
Numbers-wise, the companies they interviewed lost between 5,000 and 101,000 records, at a cost range between $750,000 and $31 million.
What was really interesting was that the average per-record cost of the loss was determined to be $204.00–and how many records does your law enforcement/public safety agency hold?
Some factors they considered in computing the cost of the breach included:
- Direct costs – communications costs, investigations and forensics costs and legal costs
- Indirect costs – lost business, public relations, and new customer acquisition costs
The report also lists a number of causes for the data breaches, such as:
- 82% of all breaches involved organizations that had experienced more than one data breach
- 42% of all breaches studied involved errors made by a third party
- 36% of all breaches studied involved lost, misplaced or stolen laptops or other mobile computing devices
- 24% of all breaches studied involved some sort of criminal or other malicious attack or act (as opposed to mere negligence).
You can download the full report here: http://www.encryptionreports.com/download/Ponemon_COB_2009_US.pdf
Thoughts and comments welcomed…r/Chuck
30.07.2009
Analysis, CJIS, data sharing, fusion center, intelligence center, Law enforcement information sharing, public safety
I had a conversation with a fusion center director yesterday about portals that really drove home a feeling I had about the recent plethora (read: boatload) of portals that the average analyst person supporting public safety and homeland security has to login to in order to do their jobs.
I’m paraphrasing a bit, but he basically indicated that the state, local, and private sector organizations in his state told him that they “DO NOT want to have to log into multiple portals” to stay informed about criminal and terrorism threats to their state’s infrastructure.”
When you take a closer look at the “Portal-mania” that exists, it seems that every agency and multiple programs within a single agency has to have their own portal for accessing the information and analytic tools that agency or program provides; here’s a quick list of ones I am familar with, (feel free to email me the names of others you know about):
- DHS HSIN State and Local Community of Interest (SLIC)
- DHS Lessons Learned Information Sharing (LLIS)
- DHS Automated Critical Asset Management System (ACAMS)
- DOJ Regional Data Exchange (R-DEx)
- DOJ National Data Exchange (N-DEx)
- DOJ eGuardian
- DOJ Law Enforcement Online (LEO)
- DOJ InfraGard
- DOJ National Sex Offender Public Website (NSOPW)
- DOJ National Criminal Intelligence Resource Center (NCIRC)
- DOJ Regional information Sharing System (RISS)
- Private Sector CyberCop
- [State] Criminal Justice Information System (CJIS)
- …add to this Department of the Treasury, Department of Transportation, and other federal agency portals
- …and about three-dozen other databases and private sector websites
This is nutz! Dedicated portals are so 1990’s…we should be able to use the same technology I used to create this website and blog (WordPress and four different plug-in widgets) to make information and advanced analytic capabilities available to Fusion Centers and other public safety users. I would like to challenge the agencies and programs listed above to make the information and capabilities they offer available through widgets, web-parts, and gadgets that Fusion Centers and other intelligence/information sharing users can integrate into THEIR portal of choice.
Whether it’s SharePoint, Oracle, or IBM Websphere, state, local, or private sector organizations should be able to pick and integrate into THEIR selected portal environment from the portal list above the information and capabilities that they need to do their job–they should not have to access the multiple, stovepiped portals as they do today.
I’d like to know what you think about this…Thanks..r/Chuck Georgo
13.07.2009
data sharing, fusion center, Information sharing, intelligence center, Law enforcement information sharing, Uncategorized
I don’t usually plug any specific software, but I felt compelled to tell you about something I have been working with Microsoft on for about the last eight months–it’s called the Fusion Core Solution (FCS). What’s different about this project is that FCS isn’t just another application, it is an effort by Microsoft to help fusion centers do more with the many applications they currently own or have plans to invest in. First a bit of background.
Whether you like the idea of a fusion center or not, they are here to stay. At last count, there were about 70 of them, and DHS recently spoke of helping to get even more going. At their core, I believe a fusion center is responsible for doing three basic things:
- Accepting and vetting reports of unusual behavior (criminal or terrorism related);
- Providing intelligence support to major case and tactical law enforcement operations; and
- Proactively supporting federal, state, and local homeland security and community safety objectives.
To do this well, the majority of fusion centers in operation today are required to rely on an assortment of manual processes, a patchwork of incompatible software applications, and dozens of disparate information sources. Walk into the typical fusion center today and you’ll probably find that an analyst answering the phone has to enter the request for their services into one application for management purposes, enter the same information into a second application for sharing purposes, then has to manually bring up and login to anywhere from 5-15 different data sources to search for information related to the service request, then has to open up at least one or more applications to write up and package up the requested response, and then, more than likely, has to either manually fax it to whomever asked for the information or call them back on the telephone to give them the answer–a pretty painful and tedious way to work.
Today though, Microsoft announced release of a project that I have been helping them to develop for quite some time–the Fusion Core Solution. Microsoft hopes, through use of Office, SharePoint and ESRI’s ArcGIS to help ease the pain described above. The FCS uses SharePoint as a horizontal integration and workflow management platform to help an analyst go from taking in a fusion center service request, to searching for information, to analyzing that information, to producing the intelligence product without having to leave the SharePoint environment at all.
At a non-technical level, the FCS will enable fusion centers to do a couple of pretty cool things:
- Provides a common look and feel across multiple analytic tools and business processes.
- Greatly reduces the number of user names and passwords analyst must remember.
- Organizes requests for fusion center services, and tracks progress of fusion center work.
- Helps to better document and comply with 28 CFR Part 23, CUI and PCII requirements.
- Provides multiple analyst-to-analyst and fusion center-to-fusion center collaboration tools
- Helps to keep track of fusion center and extended staff capabilities and availability.
From a technical perspective, FCS fully supports NIEM conformant information exchanges and establishes a framework for supporting the service-oriented principles of the Justice Reference Architecture (JRA) as it applies to information and data sharing.
In a nutshell, “Fusion Core Solution is for a Fusion Center what Microsoft Windows is to a personal computer“–you can think of FCS as the “operating system” for a Fusion Center.
For more info, check out the Fusion Core Solution website, or email me.
r/Chuck
Added 8/4/2009: Click HERE to see Joe Rozek, Microsoft’s Executive Director of Homeland Security, and Former Senior Director for Domestic Counterterrorism at The White House Office of Homeland Security talk about Fusion Core Solution
28.06.2009
data sharing, Information sharing, JIEM, law enforcement, Law enforcement information sharing, LEIS, N-DEx, NIEM, Processes, Strategy
Remember the old Reese’s Peanut Butter Cups commercial? “You got chocolate on my peanut butter “…”No, you got peanut butter on my chocolate “…? Well, this is one of these stories…
It’s no secret, the National Information Exchange Model (NIEM) is a huge success. Not only has it been embraced horizontally and vertically for law enforcement information sharing at all levels of government, but it is now spreading internationally. A check of the it.ojp.gov website lists more than 150 justice-related Information Exchange Package Documentation (IEPD) based on NIEM–it’s been adopted by N-DEX, ISE-SAR, NCIC, IJIS PMIX, NCSC, OLLEISN, and many other CAD and RMS projects.
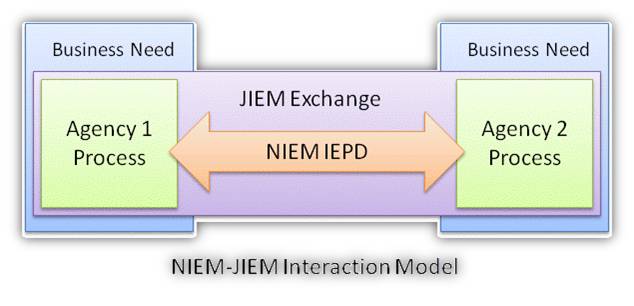
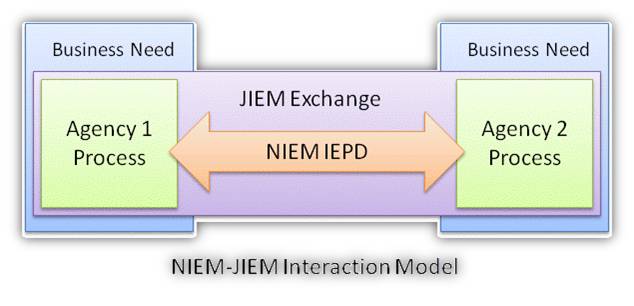
For at least the last four years, Search.org has been maintaining the Justice Information Exchange Model (JIEM) developed by Search.org. JIEM documents more than 15,000 justice information exchanges across 9 justice processes, 75 justice events, that affect 27 different justice agencies.
So if JIEM establishes the required information exchanges required in the conduct of justice system business activities, and NIEM defines the syntactic and semantic model for the data elements within those justice information exchanges…then…
Wouldn’t it make sense for JIEM exchanges to call-out specific NIEM IEPDs?
And vice-versa, wouldn’t it make sense for NIEM IEPDs to identify the specific JIEM exchanges they correspond to?
Here’s a diagram that illustrates this…
Let me know what you think..
r/Chuck
chuck@nowheretohide.org – www.nowheretohide.org
16.06.2009
data sharing, Information sharing, Law enforcement information sharing, LEIS, Uncategorized

If you haven’t heard about the Department of Health and Human Services Federal Health Architecure and CONNECT project, I suggest you pop over to this website where documentation for version 2.0 of the software resides:
http://www.connectopensource.org/display/NHINR2/Release+2.0+Home
CONNECT is an open source software gateway that connects public and private health orgaizations to the National Health Information Network. Think of it like a giant peer-to-peer N-DEx, but with an open source “front-porch” that drops into each agency and extracts the data from back-end systems.
I’ll be doing more investigation into the CONNECT project to see if we can adapt it for law enforcement information sharing use–the closest thing to this on the LEIS side is the FINDER project in orlando, FL.
as always, comments and thoughts welcomed.
r/Chuck
chuck@nowheretohide.org – www.nowheretohide.org
 Hi everyone,
Hi everyone, So it’s no great revelation that public safety has benefited greatly from public private partnerships, and I’m cool with that, especially when we are dealing with technology that saves lives. However, a press release hit my email inbox today that made me think of the risks to security and privacy when we implement innovative technologies.
So it’s no great revelation that public safety has benefited greatly from public private partnerships, and I’m cool with that, especially when we are dealing with technology that saves lives. However, a press release hit my email inbox today that made me think of the risks to security and privacy when we implement innovative technologies.